In the decentralized landscapes of Web3, where anonymity clashes with the need for trust, zero knowledge proof of humanity emerges as a cornerstone for secure interactions. Traditional identity systems expose users to data breaches and surveillance, but zk proofs offer a methodical path forward: verifying human uniqueness without surrendering personal details. This privacy-first approach counters Sybil attacks, enabling fair governance and equitable resource distribution in protocols like airdrops and DAOs.
Consider the vulnerabilities in current setups. Bots and fake accounts dilute community value, while centralized verifiers hoard biometric data ripe for exploitation. ZK proofs flip this script, allowing provers to demonstrate truths - such as 'I am a unique human' - solely through mathematical conviction, revealing nothing extraneous. This aligns with Web3's ethos: user sovereignty preserved amid scalability demands.
Decoding Zero-Knowledge Proofs for Identity Primitives
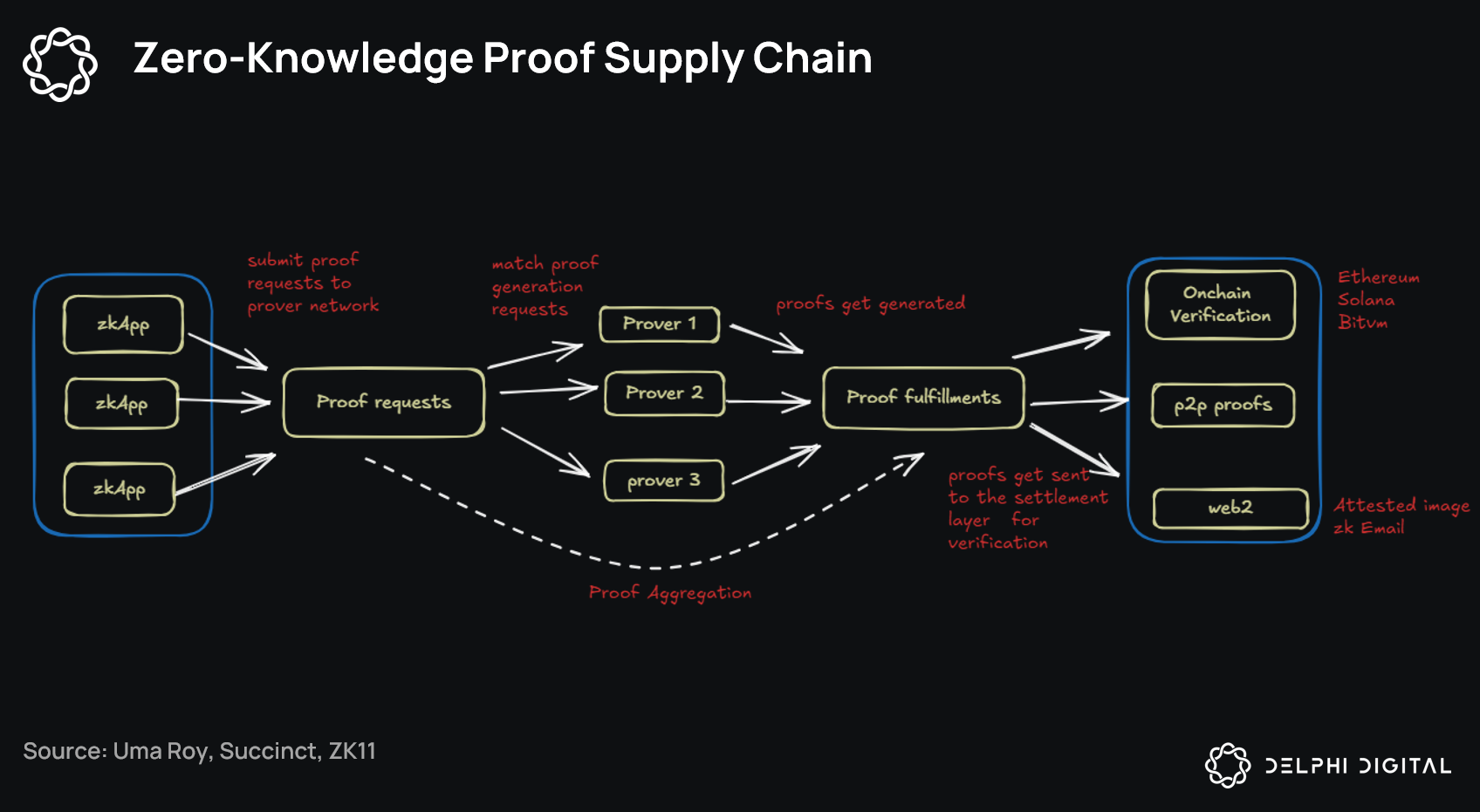
At their core, zk proofs proof of humanity rely on cryptographic protocols where a prover convinces a verifier of a statement's validity without disclosing underlying data. Picture a locked box containing proof of your palm scan or email verification; you show the box seals match, but never open it. Protocols like zk-SNARKs and zk-STARKs compress this into succinct, verifiable computations on blockchains.
Methodically, the process unfolds in three phases: setup, where public parameters are generated; proving, crafting the zero-knowledge argument; and verification, a quick check on-chain. For zk identity verification, this means attesting attributes like age or residency via hashed credentials. No more repetitive KYC hurdles; once proven, credentials reuse across dApps.
Zero-knowledge proofs let you prove a statement is true without revealing anything beyond the truth of that statement.
This efficiency scales to millions, vital for mass adoption. Yet, conservative deployment tempers hype: computational intensity demands Layer 2 optimizations, as seen in Polygon's zkEVM.
Humanity Protocol: Pioneering On-Chain Biometric ZK Verification
Humanity Protocol stands as a rigorous example, layering palm recognition with ZKPs on a Layer 2 chain. Users scan palms via mobile, generating a hashed Human ID; no raw biometrics stored, just verifiable proofs. This yields sybil resistant zk credentials for UBI, governance, and airdrops, all privacy intact.
Dual verification - device-bound and behavior signals - minimizes spoofing risks. Developers integrate via SDKs, issuing souls (identity tokens) for seamless dApp use. In volatile Web3 markets, this methodical sybil resistance preserves protocol integrity, much like duration matching stabilizes bond portfolios against rate swings.
Read how zero-knowledge proofs enable private and trustless identity verification in Web3 for deeper mechanics.
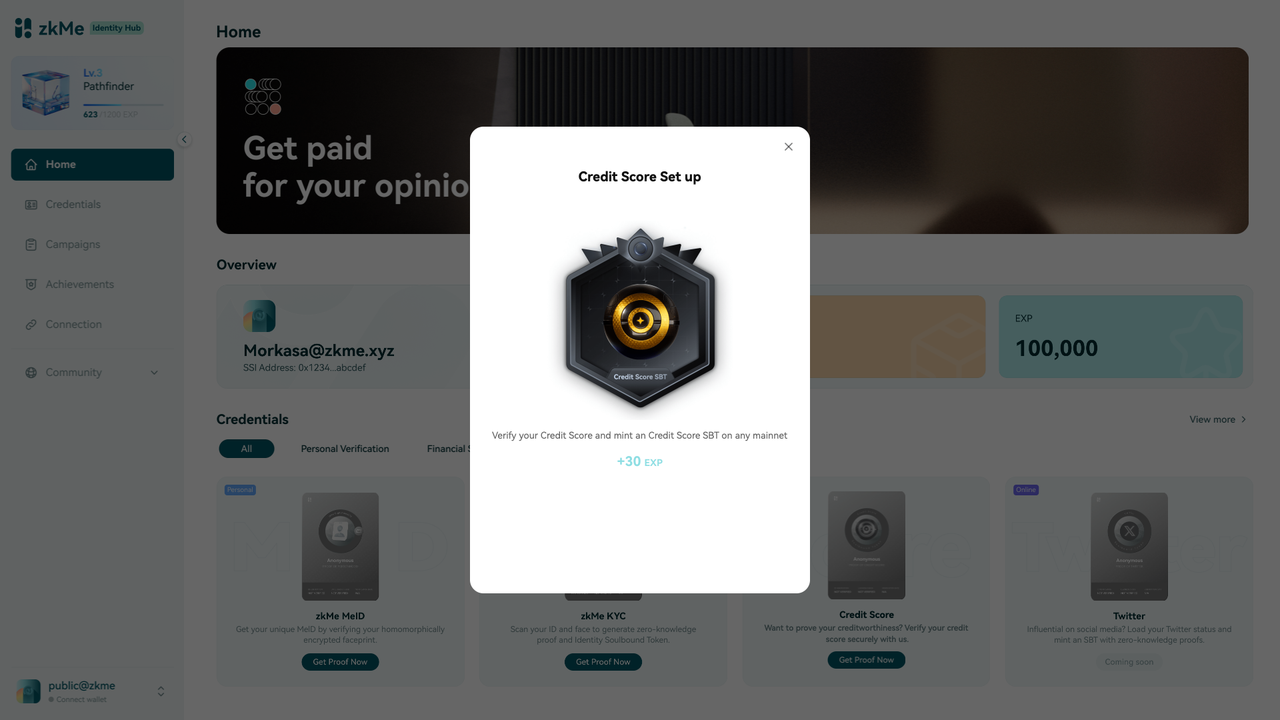
zkMe and Self: Expanding ZK Horizons in Compliance and DeFi
zkMe advances with zkKYC, proving compliance attributes - citizenship, age - sans specifics. Financial institutions meet regs while users retain opacity, a balanced risk-reward akin to credit spreads in fixed income.
Self integrates zk PoH into Aave, boosting yields for proven humans. This incentivizes verification, fortifying DeFi against exploits. Together, these protocols signal a maturing ecosystem: privacy proof of humanity web3 isn't fringe; it's foundational for sustainable growth.
Challenges persist, from proof generation latency to oracle dependencies, but iterative refinements promise resilience. As adoption swells, expect zk proofs to underpin fairer, fortified networks.
Overcoming these hurdles requires disciplined engineering, much like calibrating credit risk models to withstand economic downturns. Recent advancements in recursive proofs and hardware acceleration are slashing generation times, paving the way for real-time verifications in high-throughput environments.
Comparative Edge: Leading ZK Proof of Humanity Protocols
Scrutinizing protocols side-by-side reveals distinct risk profiles and strengths. Humanity Protocol excels in biometric depth with palm scans hashed into Human IDs, ideal for UBI schemes demanding ironclad uniqueness. zkMe prioritizes regulatory alignment through zkKYC, proving attributes like age without granular exposure - a prudent hedge against compliance volatility. Self's Aave integration demonstrates practical yield incentives, doubling returns for verified users and underscoring economic motivations in adoption.
Comparison of Leading ZK PoH Protocols: Humanity, zkMe, and Self
| Protocol | Verification Method | Key Use Cases | Privacy Features | Integrations |
|---|---|---|---|---|
| Humanity Protocol | Dual-layer biometrics (palm recognition) + ZKPs | Sybil-resistant apps, fair governance, on-chain UBI | Biometric hash tied to Human ID verified via ZKPs; user data control; reusable credentials | Polygon zkEVM, dApps |
| zkMe | zkKYC attributes via ZKPs | Proving age/citizenship for compliance without exposing details | No revelation of underlying personal information | zk-Credential Network |
| Self | ZK Proof-of-Humanity | PoH yield boost (e.g., double yield on Aave) | Unique identity validation without revealing personal info | Aave |
These solutions collectively fortify sybil resistant zk credentials, mitigating bot swarms that erode DAO votes and airdrop fairness. In my view, blending biometrics with behavioral signals, as in Humanity Protocol, offers the most conservative path to scalability, minimizing false positives akin to tightening duration bands in fixed income portfolios.
Key Advantages of ZK PoH
- Privacy preservation without data exposure, as in Humanity Protocol using ZKPs with palm biometrics.

- Sybil resistance for fair governance, like Self's Aave integration doubling yields for verified humans.
- Reusable credentials across dApps, enabling one-time verification in Humanity Protocol.

- Compliance-friendly attribute proofs, such as zkMe's zkKYC for age or citizenship without revealing details.
- Scalable on L2 chains like zkEVM, powering Humanity Protocol's on-chain UBI.

Real-World Deployments: From DeFi Yields to Governance Safeguards
Self's partnership with Aave exemplifies tangible impact: verified humans access enhanced yields, curbing exploitation while rewarding authenticity. zkMe's zkKYC streamlines onboarding for Web3 finance, where proving 'over 18' suffices without ID leaks. Meanwhile, emerging tools like zkProofers and ZK Email Stamps from Human Passport leverage everyday proofs - Amazon deliveries or Uber rides - to incrementally build humanity scores, fostering organic verification without heavy biometrics.
This modular approach suits diverse ecosystems. Developers at platforms like ZKHubs. com can plug in these primitives, crafting zk identity verification layers that scale with user bases. Conservative estimates suggest PoH adoption could slash Sybil-induced losses by 70% in governance protocols, preserving capital in community treasuries.
Yet, vigilance remains paramount. Oracle risks in off-chain signals demand audited circuits, and interoperability standards like ERC-7739 will unify credential formats. As Web3 matures, privacy proof of humanity web3 protocols will underpin trustless economies, where verification feels invisible, not invasive. Stakeholders prioritizing these tools position themselves for enduring resilience amid protocol evolutions.
ZKHubs. com leads in curating such solutions, empowering builders with zk identity management that balances privacy and verifiability. The trajectory points to a future where human uniqueness bolsters decentralized systems without the shadows of centralized oversight.








No comments yet. Be the first to share your thoughts!