In the evolving landscape of Web3 identity systems, zk proof of humanity emerges as a cornerstone for balancing privacy with verifiable uniqueness. Traditional identity verification often demands invasive data sharing, exposing users to surveillance and data breaches. Zero-knowledge proofs (ZKPs) flip this paradigm, allowing individuals to attest to their singular human status without revealing biometric details or personal history. This methodical approach not only fortifies proof of personhood zk but also underpins Sybil-resistant mechanisms essential for fair airdrops, governance, and decentralized finance.

Consider the vulnerabilities in current systems. Centralized platforms hoard sensitive data, while basic blockchain addresses fail to distinguish humans from bots. Enter ZKPs: cryptographic primitives where a prover convinces a verifier of a statement's truth without extraneous information leakage. For zk identity verification, this means palm scans or behavioral signals transform into compact proofs, verifiable on-chain yet privacy-preserving off-chain.
Overcoming Sybil Attacks Through Privacy-First Verification
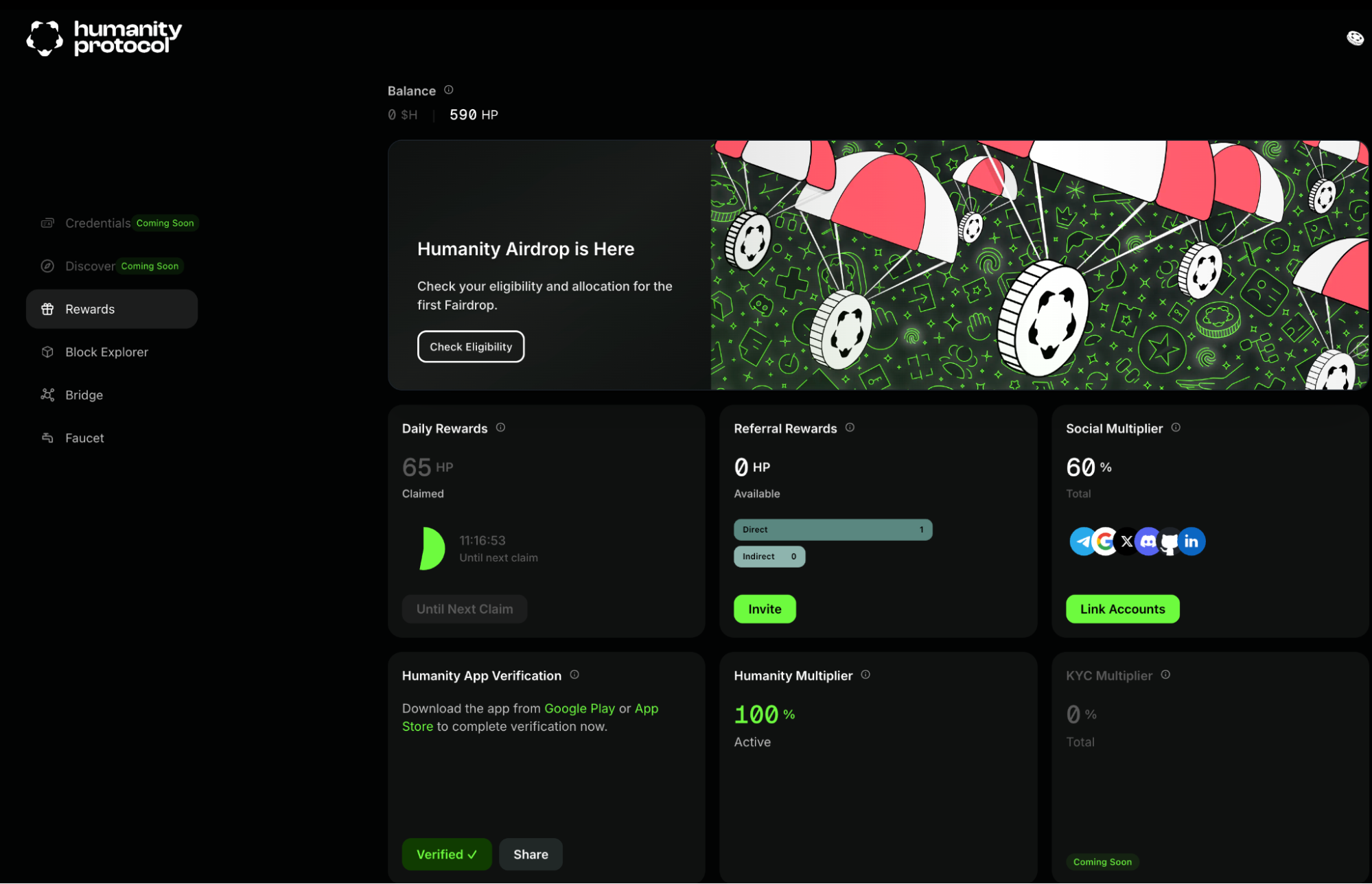
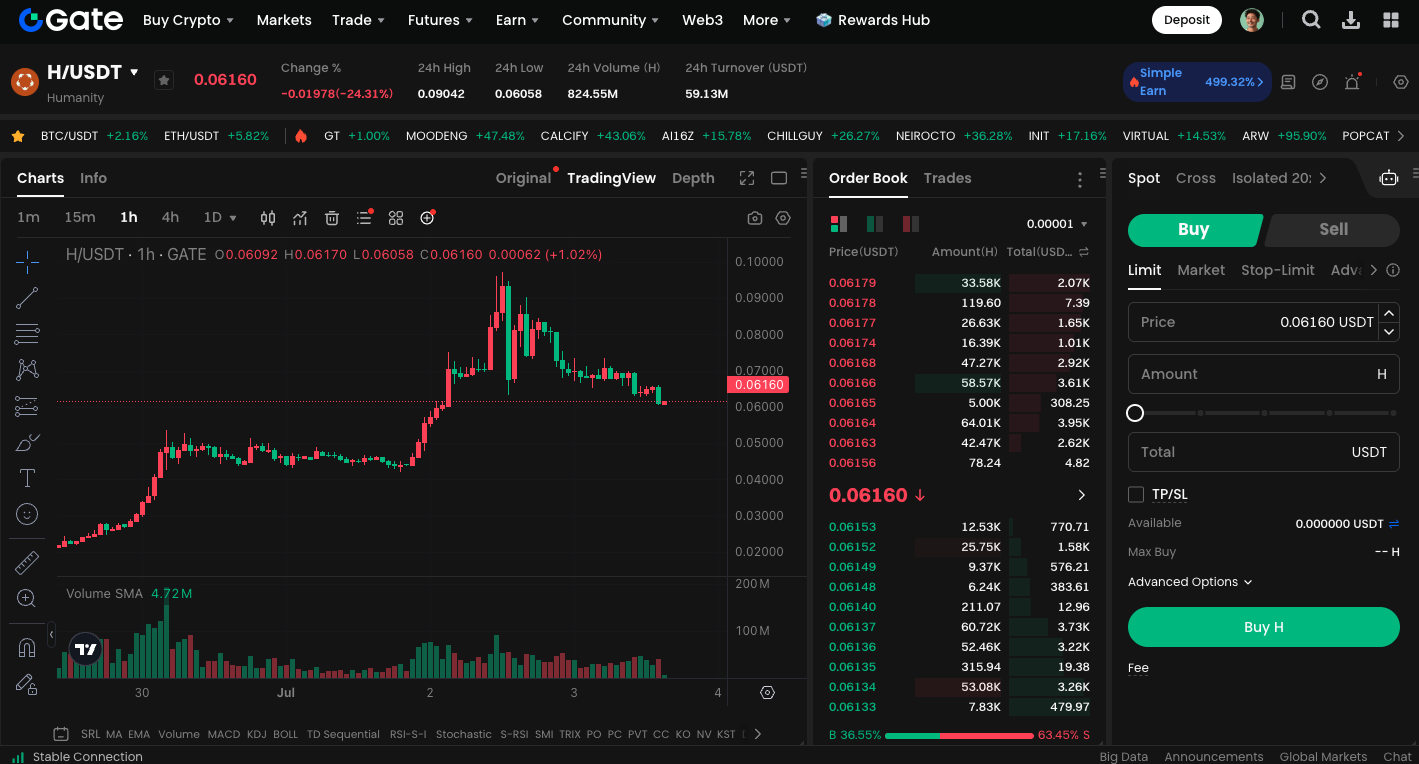
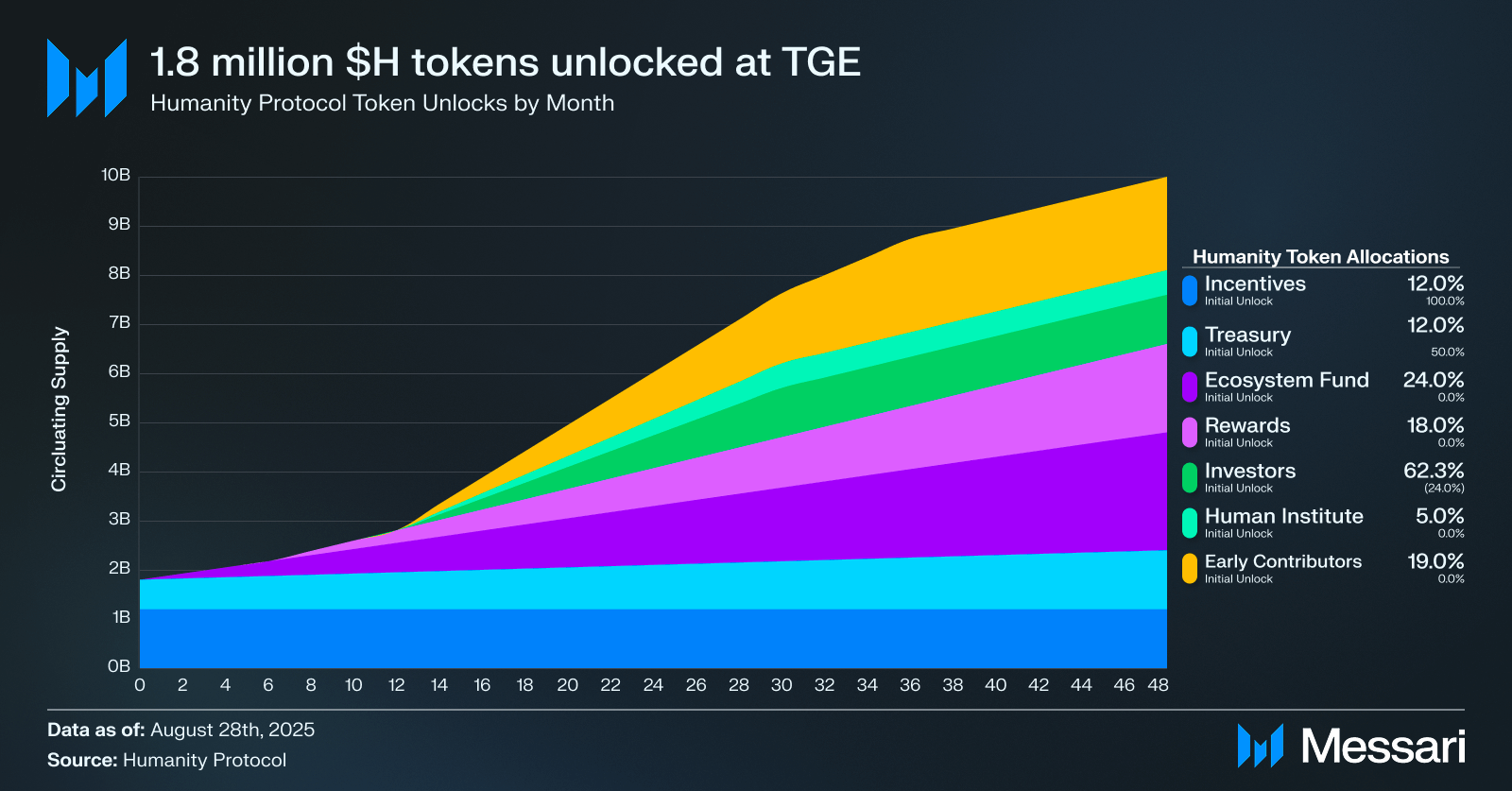
Sybil attacks plague decentralized networks, where one entity masquerades as many to manipulate votes or claims. Privacy proof of humanity via ZK addresses this head-on. Protocols like Humanity Protocol employ dual-layer biometrics: a palm scan generates a unique identifier, processed through ZKPs by a network of zkProofer nodes. These nodes validate without storing data, ensuring each proof ties to a distinct human. Rewards in native tokens incentivize participation, creating a robust, decentralized oracle for humanity checks.
Key ZK PoH Features
- Palm Biometrics: Users scan their palm to generate a unique identifier, verified via ZK proofs without storing or exposing biometric data. (Humanity Protocol)
- zkProofer Nodes: Decentralized network of nodes validates ZK proofs, ensuring secure and distributed verification. (Humanity Protocol)
- Sybil Resistance: Prevents multiple fake identities by confirming each participant as a distinct human via ZKPs.

- Token Incentives: Participants earn native tokens for contributing to proof validation and network security. (Humanity Protocol)
- Airdrop & DAO Applications: Enables Sybil-resistant airdrops, private DAO voting, and compliance without revealing identities.

This setup extends to applications demanding trust without exposure. Private DAO voting becomes feasible, as members prove uniqueness anonymously. Regulatory compliance follows suit, with attestations satisfying KYC mandates minus data retention risks. Self Protocol's integration with Google Cloud exemplifies scalability, serving millions via ZKP-based tools that embed seamlessly into AI and Web3 platforms.
Technical Foundations of ZK in Credential Systems
At the core lie zk-SNARKs and zk-STARKs, tailored for efficiency in zk credentials blockchain. zk-SNARKs yield compact proofs ideal for on-chain verification, though trusted setups pose risks. zk-STARKs counter with transparency and quantum resistance, albeit larger proofs demand optimized circuits. Developer guides, such as those from ChainScore Labs, detail circuit design for private credential sharing: encode claims into arithmetic circuits, generate proofs via provers like Groth16, and verify with minimal gas.
ZKPs enable users to prove group membership or humanity without doxxing themselves, a game-changer for Web3 anonymity.
Semaphore from Ethereum's Privacy Stewards offers a practical lens: users signal endorsements or votes as group members, identities shielded. Evaluations show zk-SNARKs excelling in proof size, vital for mobile Web3 users. Yet, methodical deployment matters; poor circuit design balloons costs, underscoring the need for audited libraries from curated ZK repositories on GitHub.
zkMe advances this with a credential network, issuing verifiable claims under privacy-by-design. Users disclose only necessary attributes, like age over 18, via selective proofs. This granular control empowers dApps, from lending protocols assessing creditworthiness anonymously to social platforms curbing spam.
Real-world deployments highlight the practicality of these systems. Human Passport's developer platform equips builders with tools for community protection, integrating proof of personhood zk to filter bots without invasive checks. QuickNode's builder guides emphasize such mechanisms, ensuring digital identities map to unique humans via ZK layers.
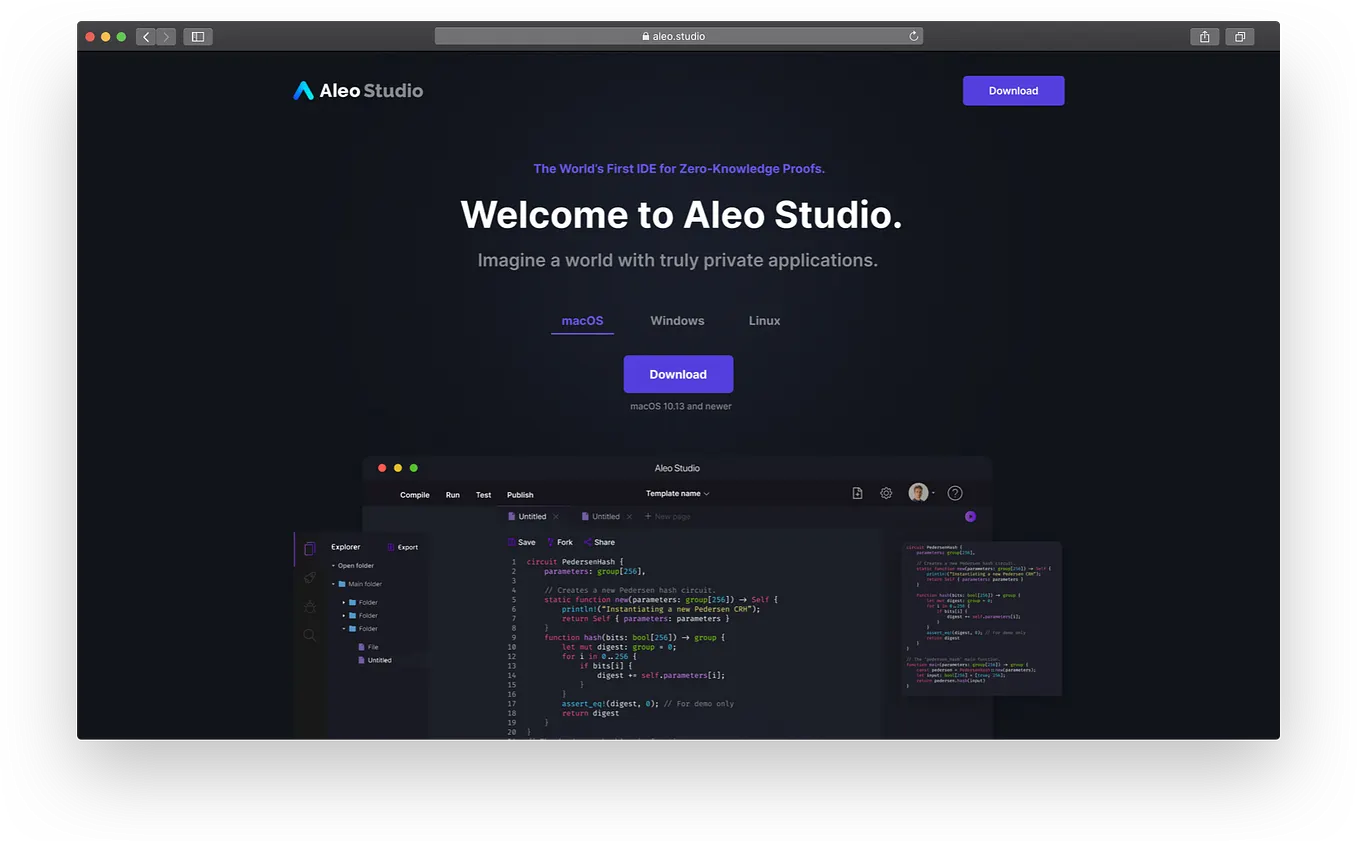
Polkadot's 2025 advancements secure relaying with ZK proofs atop the ELVES protocol, demonstrating cross-chain viability for zero knowledge proof humanity. Meanwhile, zkML in ERC-8004 standards proves model correctness on-chain, extending ZK to AI agents in identity contexts. These evolutions address efficiency trade-offs methodically: zk-SNARKs minimize on-chain footprint for high-throughput apps, while zk-STARKs prioritize post-quantum security amid rising threats.
Navigating Implementation Challenges
Deploying ZK for privacy proof of humanity demands rigor. Circuit complexity can spike proof generation times, deterring mobile adoption. Trusted setups in SNARKs introduce ceremony risks, mitigated by multi-party computations yet never fully erased. My view: prioritize STARKs for long-term resilience, accepting short-term gas premiums as capital preservation in volatile chains.
Essential ZK PoH Developer Resources
- Awesome ZKP (GitHub): Curated list of ZK papers, tools, libraries. View Repo

- ChainScore Labs Circuit Guide: Guide to ZK-SNARKs for private credential sharing. Read Guide

- Semaphore: ZK protocol for private group membership proofs. Docs

- zkMe Credential Network: ZKP-based privacy-preserving credentials. Site

- delendum-xyz ZK Knowledge Base: Comprehensive ZK resources. GitHub
Curated repositories like GitHub's awesome ZK list and delendum-xyz's knowledge base arm developers with audited libraries. Gate. com's landscape overview maps principles to applications, from privacy tech to scalable verification. Yet, success hinges on optimization: profile circuits, leverage hardware accelerators, and test verifier gas exhaustively.
Selective disclosure via ZK turns identity into a toolkit, not a liability.
Consider a lending dApp: borrowers prove credit score ranges without full history, reducing default risks while shielding data. Social DAOs vote privately, curbing collusion. This granular control, powered by protocols like zkMe, fosters ecosystems where privacy fuels utility.
Looking ahead, interoperability looms large. Standards like ERC-8004 and Polkadot integrations promise seamless ZK flows across chains. Partnerships, such as Self Protocol with Google Cloud, scale to millions, embedding zk identity verification in AI-driven services. Humanity Protocol's zkProofer nodes evolve into global oracles, rewarding honest validation.
Builders must weigh trade-offs conservatively: SNARK speed versus STARK transparency. Resources abound, from developer docs to efficiency studies, guiding methodical builds. Ultimately, ZK proofs redefine Web3 identity, proving humanity's uniqueness without surrender. Privacy endures as the bedrock, enabling trust in decentralized frontiers.






No comments yet. Be the first to share your thoughts!