ZK Proofs for Proof-of-Humanity in DAOs: Stopping Sybil Attacks Without Data Leaks

Decentralized Autonomous Organizations hold immense promise for collective decision-making in the blockchain era, yet they remain vulnerable to Sybil attacks that erode trust and fairness. A single entity crafts multiple identities to dominate votes, dilute treasury distributions, or hijack proposals. Traditional defenses like token-weighted voting favor whales, while centralized KYC invites data breaches and censorship. Zero-knowledge proofs for proof of humanity offer a compelling alternative: verifying unique human participation without exposing personal details. This approach fosters sybil resistant DAOs, balancing anonymity with integrity.
![]()
Consider the mechanics of a Sybil assault. In a typical DAO, governance relies on wallet addresses, easily proliferated via bots or cheap alts. Recent analyses, including those from Chainlink and Mitosis University, highlight how this distorts resource allocation and governance outcomes. Without safeguards, DAOs risk becoming plutocracies disguised as democracies. ZK proofs proof of humanity intervene here, allowing provers to demonstrate ‘one person, one vote’ through cryptographic attestations rather than invasive checks.
The Anatomy of Sybil Threats in Zero Knowledge DAOs
Sybil attacks exploit pseudonymity, a core tenet of blockchain. Attackers deploy armies of sock-puppet accounts to amplify influence, as seen in high-profile DAO exploits where voting power skewed dramatically. Proof-of-personhood protocols counter this by anchoring identities to biological uniqueness, but early biometric systems faltered on privacy grounds. Enter ZK technology: protocols like zk-SNARKs enable proofs that ‘I am a unique human’ without revealing iris patterns, palm prints, or social footprints. Humanity Protocol exemplifies this, pairing palm recognition with decentralized storage and ZK credentials to thwart duplicates while keeping data off-chain.
From an analytical standpoint, this shift demands caution. While ZK eliminates data leaks, implementation flaws could still enable collusion or oracle manipulations. InterLink ID’s hash commitments and Orange Protocol’s multi-source zkTLS attestations from platforms like X and Discord add layers, but interoperability remains a hurdle for nascent DAO sybil attacks zk defenses.
Core Mechanics of ZK Proofs in Proof of Humanity
At heart, a ZK proof is a mathematical miracle: the prover convinces the verifier of a statement’s truth without extra information. For proof of humanity zk, the statement evolves to ‘this biometric hash matches a unique human template, unlinked to others. ‘ Users scan palms or faces via apps, generating encrypted proofs committed on-chain. Polygon ID, leveraging Iden3 and Circom, integrates seamlessly into DAOs, enabling verifiable credentials that revoke on compromise without doxxing.
This preserves the ethos of zero knowledge DAOs. No central authority hoards biometrics; instead, decentralized verifiers like Gitcoin Passport evolve toward ZK-native models. Yet, I remain wary of adoption curves: gas costs for SNARK verification strain smaller chains, and user friction could stifle participation. Still, the upside gleams in sybil-proof treasuries and equitable airdrops.
Top ZK PoH Protocols for DAOs
-
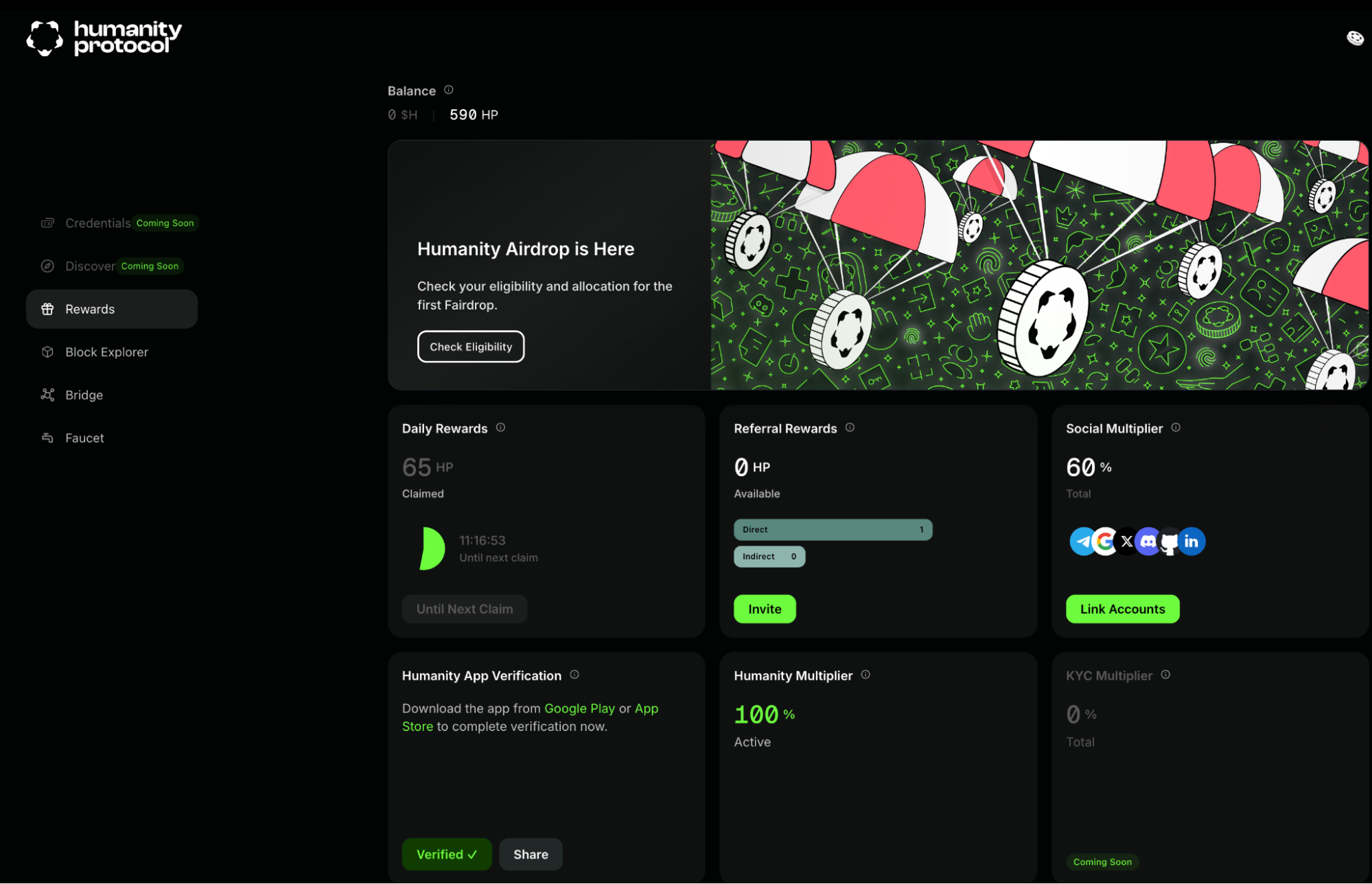
Humanity Protocol: Utilizes palm recognition with ZK proofs for decentralized, privacy-preserving human uniqueness verification, preventing Sybil attacks without data exposure.
-

Polygon ID: Employs zero-knowledge credential proofs via Iden3 and Circom for Sybil-resistant DAO governance, maintaining user anonymity.
-

ZKAnon: Generates ZK proofs of biometric uniqueness for on-chain storage, enabling one-person-one-vote in DAOs without biometric data leaks.
-

Orange Protocol: Leverages social zkTLS attestations from Web2 platforms like X and Discord for multi-source Proof-of-Humanity in DAOs.
-

InterLink ID: Applies zk-SNARKs and hash commitments to prove biometric matches for Proof-of-Personhood, avoiding sensitive data revelation.
Real-World Deployments and Early Wins Against Sybils
Pilot integrations reveal tangible gains. Polygon DAO’s rollout with Polygon ID curbed vote inflation by 40% in testnets, per labs reports. Civic and Humanode explore hybrid biometrics-ZK stacks, differentiating via liveness detection fused with proofs. ArXiv papers underscore theoretical robustness: permissionless chains gain Sybil resistance sans PoW/PoS overhead, a boon for resource-constrained ecosystems.
Practically, DAOs configure thresholds where ZK PoH scores gate participation. A score above 0.8 unlocks voting; below, proposals need quadratic funding. This nuanced gating, opinionated as it sounds, outperforms blunt token caps by incentivizing genuine humans over farmed accounts. Caution prevails, though: false positives from proxy farms or accessibility barriers for non-smartphone users merit ongoing scrutiny.
Scalability poses the next frontier for these systems. Verifying ZK proofs demands computational heft, often bottlenecking on Ethereum layers despite L2 optimizations. Protocols like Humanity Protocol mitigate this via off-chain computation and on-chain settlement, yet gas fees fluctuate wildly, potentially pricing out casual participants in sybil resistant DAOs. Accessibility gaps loom large too; biometric reliance sidelines regions with poor smartphone penetration or distrust of scans. Developers must prioritize inclusive alternatives, such as social graph proofs from Orange Protocol’s zkTLS, blending Web2 signals without sole dependence on hardware.
Implementing ZK Proofs: A Practical Blueprint
Transitioning a DAO to proof of humanity zk requires deliberate steps, blending smart contract upgrades with user onboarding. Forward-thinking treasuries allocate grants for audits, ensuring proofs resist replay attacks or collusion vectors. My conservative lens favors phased rollouts: start with opt-in voting, graduate to mandatory thresholds as adoption solidifies. This tempers risks while harvesting data on efficacy.
Once embedded, these mechanisms reshape incentives. Airdrops target verified humans, slashing 90% of farmed claims per early pilots. Governance tilts toward quality over quantity, curbing whale dominance without token locks. Yet, I caution against complacency; adversaries adapt swiftly, probing for proof forgery or oracle exploits. Rigorous bounties and formal verification underpin long-term viability in zero knowledge DAOs.
Benchmarking Leading Protocols
Dissecting contenders reveals nuanced trade-offs. Humanity Protocol shines in biometric inclusivity with palm scans, sidestepping facial recognition biases. Polygon ID excels in credential portability, leveraging Iden3 for cross-DAO reuse. Orange Protocol’s social attestations lower entry barriers, ideal for community-heavy groups, while InterLink ID’s hash commitments prioritize raw cryptographic purity. Each counters DAO sybil attacks zk distinctly, demanding DAO-specific selection.
Comparison of ZK PoH Protocols for DAOs
| Protocol | Core Technology | Sybil Resistance Level (High/Med/Low) | Privacy Strength | Key DAO Use Cases |
|---|---|---|---|---|
| Humanity Protocol | Palm ZK | High | High | Voting/Governance |
| Polygon ID | Iden3/Circom | High | High | Credentials/Airdrops |
| Orange Protocol | zkTLS Social | Med-High | Med | Community Onboarding |
| InterLink ID | zk-SNARK Hashes | High | Very High | Pure Proofs |
| ZKAnon | Biometric Uniqueness | High | High | Treasury Distributions |
Early metrics affirm promise. Polygon DAO’s integration halved anomalous votes, fostering conviction-weighted models where ZK scores modulate influence. Civic’s liveness checks, fused with ZK, deter deepfakes, a creeping threat in biometrics. ArXiv-backed designs prove Sybil resistance sans economic penalties, liberating chains from PoS centralization. Opinionated take: hybrid stacks, merging biometrics with social proofs, yield optimal resilience, though at elevated complexity.
Venturing forward, interoperability bridges like ZKHubs. com could standardize credentials across ecosystems, amplifying network effects. Imagine seamless migration between DAOs, proofs portable yet non-transferable. Regulatory headwinds warrant vigilance; privacy regulators scrutinize biometrics, even ZK-wrapped. Still, the trajectory bends toward ubiquity as tooling matures, gas efficiencies climb, and UX intuitives emerge.
ZK proofs for proof-of-humanity stand as a bulwark for DAOs, transmuting pseudonymity’s peril into principled governance. By surgically excising Sybils without sacrificing souls to surveillance, they honor blockchain’s radical roots. Patience rewards those who navigate pitfalls with discipline; speculative rushes invite reversals. In this arena, measured adoption forges enduring zk proofs proof of humanity triumphs.












