ZK Proofs for Proof of Humanity: Privacy-Preserving Human Verification in Web3

In the decentralized landscapes of Web3, verifying human presence without exposing personal details has become a cornerstone challenge. Traditional methods falter under scrutiny; they either demand invasive data sharing or succumb to manipulation by bots and Sybil clusters. Enter ZK proofs for proof of humanity, a methodical cryptographic shield that affirms uniqueness while safeguarding privacy. This approach, blending zero-knowledge proofs with biometric anchors, fortifies networks against fraud without compromising user autonomy.

Sybil attacks erode trust in blockchain ecosystems. A single adversary spins countless pseudonymous identities, inflating voting power, draining airdrops, or skewing governance. Protocols without robust defenses witness wallet farms proliferating unchecked. Here, proof of humanity zk intervenes decisively, curtailing such exploits through verifiable human signals. Recent advancements underscore this shift; networks now prioritize sybil resistance as a foundational layer, much like capital preservation in turbulent markets.
Sybil Resistance: The Bedrock of Trustworthy Web3 Interactions
Consider the mechanics of disruption. Bots masquerade as users, siphoning resources meant for genuine participants. Faucets, grants, and DAOs suffer most acutely. ZK identity sybil resistance counters this by enabling proofs of uniqueness. Users attest to their singular humanity via zero-knowledge circuits, revealing nothing beyond the claim’s validity. This elegance stems from ZKPs’ core tenet: prove a statement true without disclosing underlying data.
Humanity Protocol exemplifies this rigor. Its zkProofers, specialized nodes in the Proof of Humanity consensus, validate biometrics like palm scans through ZK layers. No central authority hoards sensitive info; instead, decentralized verifiers ensure tamper-proof outcomes. The result? Ecosystems purged of duplicates, fortified against wallet farms and botnets.
Key Advantages of ZK PoH
-
Eliminates Sybil Attacks via biometric ZK uniqueness proofs, as in Humanity Protocol‘s palm biometrics.
-
Preserves Privacy by revealing no personal data, core to ZKPs in protocols like zkTLS.
-
Scales for dApps with seamless integration, e.g., zkTLS requires no infrastructure changes.
-
Enhances Governance Fairness by ensuring one human, one vote through ZK proof of personhood.
-
Bolsters Airdrop Security against wallet farms, as with Human Passport in 120+ projects.
Zero-Knowledge Proofs: Precision Tools for Human Verification
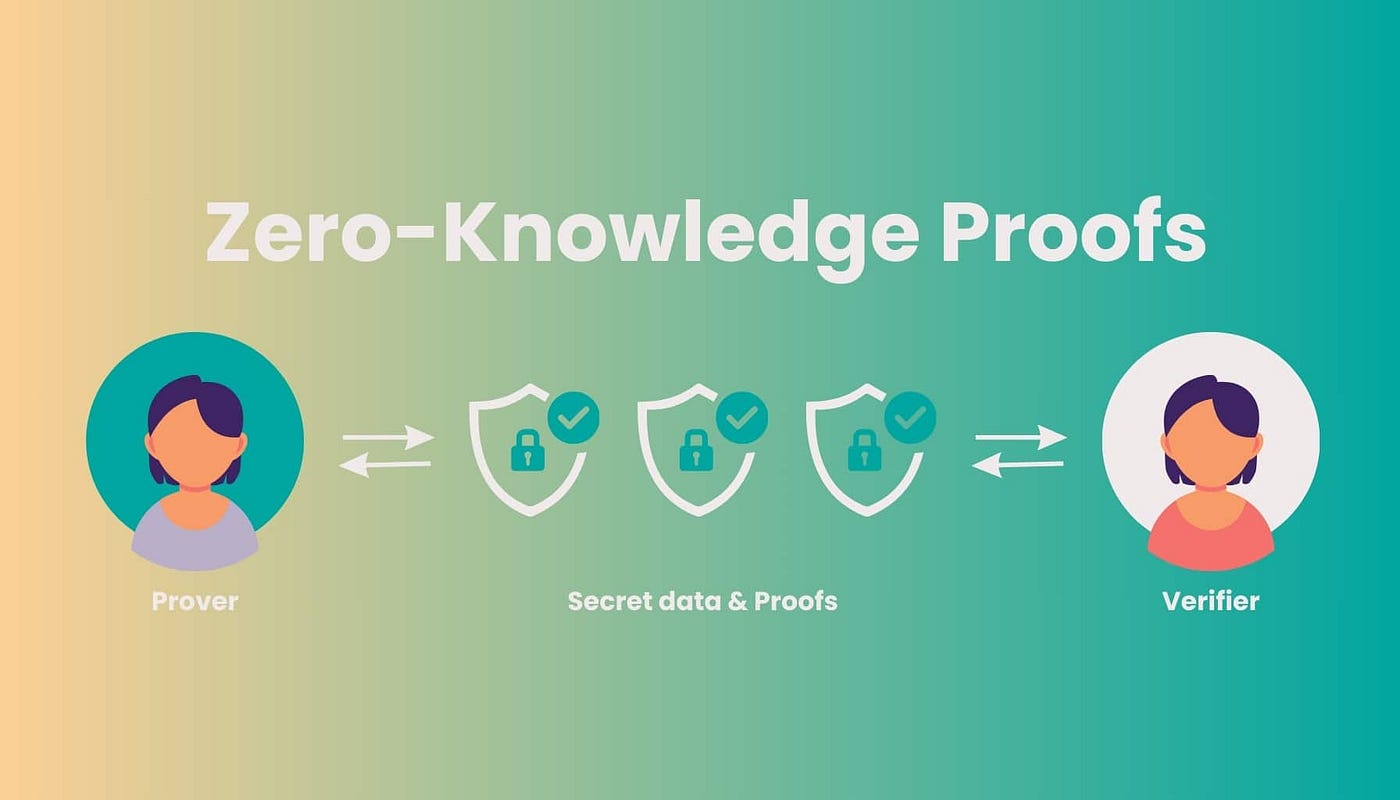
At their essence, ZKPs empower a prover to convince a verifier of a fact’s truth sans evidentiary disclosure. In zero knowledge proof human verification, this translates to confirming “I am a unique human” without broadcasting biometrics or credentials. Mathematical constructs like zk-SNARKs or zk-STARKs underpin these proofs, compressing complex attestations into succinct, verifiable tokens.
This methodology aligns with Web3’s privacy ethos. Users retain sovereignty over their data, sharing only what’s necessary. zkTLS extends this paradigm, allowing proofs of secure website access without content exposure. Imagine attesting to KYC completion on a trusted platform, all while veiling specifics. Such innovations render traditional OAuth relics, obsolete in privacy-first paradigms.
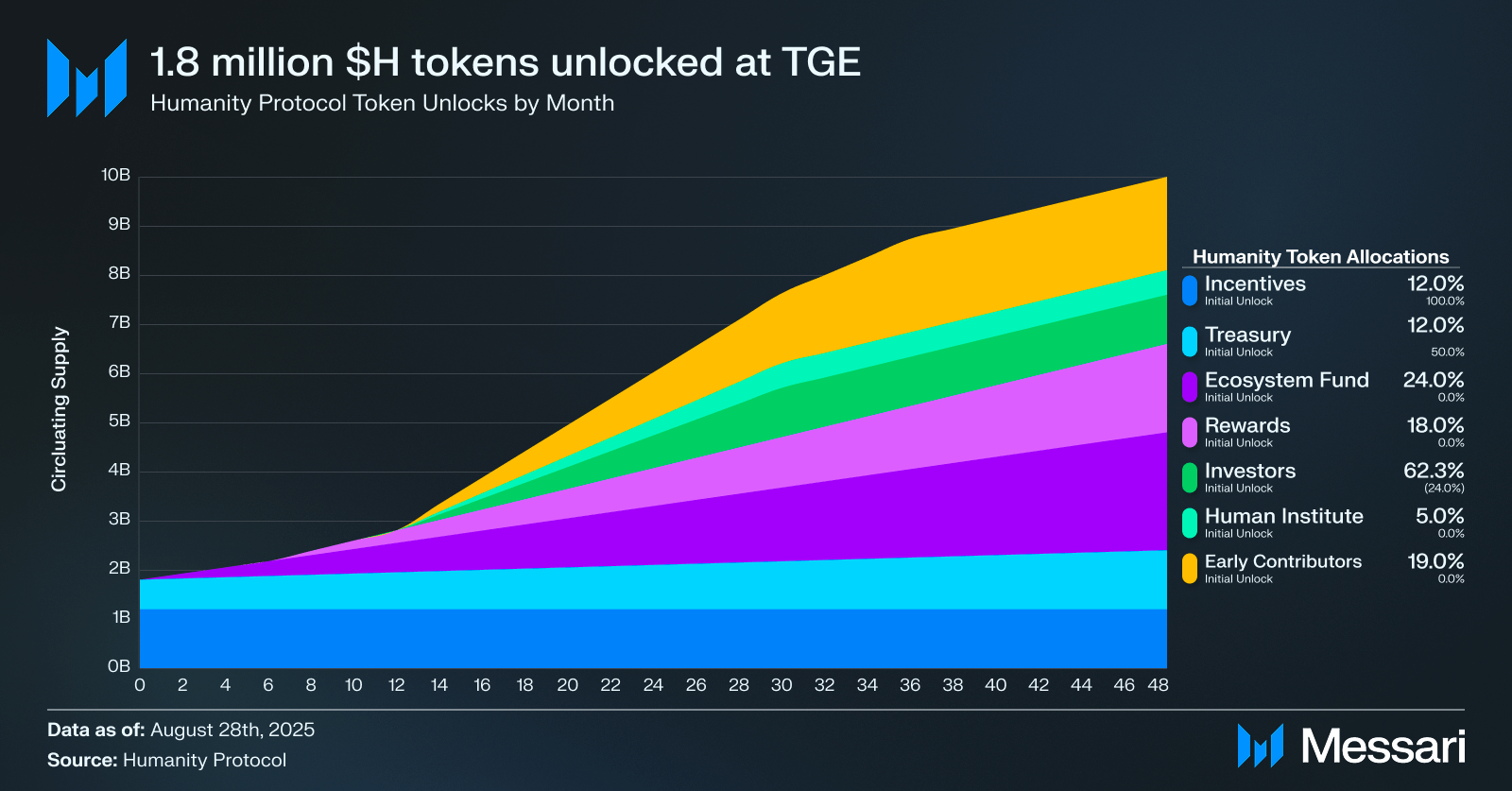
Yet, implementation demands caution. Conservative deployment favors hybrid models: biometrics for enrollment, ZK for ongoing proofs. Humanity Protocol’s dual-layer system, incorporating fingerprint and facial cues, generates these attestations. Its H token incentivizes verifiers, weaving economic alignment into technical robustness.
Humanity Protocol and Ecosystem Pioneers in Action
Humanity Protocol stands as a beacon, leveraging palm recognition fused with ZKPs for decentralized trust. Users scan palms at verification hubs; ZK circuits then mint proofs of uniqueness. These circulate network-wide, underpinning applications from faucets to voting. zkProofers orchestrate this ballet, validating claims methodically to thwart collusion.
Beyond, Rarimo’s aggregator unites Unstoppable Domains, Gitcoin Passport, and Civic. Their Proof of Humanity plug-in deploys ZK proofs across dApps, verifying humans sans bots. Self Protocol integrates similarly, shielding Google Cloud Web3 faucets from sybil incursions. Human Passport toolkit, adopted by over 120 projects, detects duplicates proactively.
These protocols do not merely react; they anticipate. By embedding privacy proof of humanity web3 natively, they recalibrate incentives. Bots lose efficacy; humans command premium trust. Developers gain tools for seamless PoP integration, from oracle feeds to DeFi access gates. The trajectory points toward ubiquitous adoption, where every interaction presumes verified personhood.
Scalability remains a measured concern. ZK proof generation, while efficient, burdens mobile devices during peak loads. Protocols mitigate this through off-chain computation and layered consensus, as seen in Humanity Protocol’s zkProofers. These nodes distribute verification, ensuring proofs propagate swiftly across chains without bottlenecks. Developers must weigh gas costs against privacy gains, opting for succinct zk-SNARKs where transparency demands zk-STARKs.
Challenges and Measured Solutionsin ZK Proof of Humanity Deployment
Adoption hinges on frictionless onboarding. Biometric scans intimidate privacy purists, yet ZK layers neutralize risks by ephemeralizing data post-proof. Human Passport addresses this with lightweight toolkits, empowering 120 and projects to embed zk identity sybil resistance sans overhauls. Self Protocol’s faucet integrations exemplify practicality; Google Cloud Web3 testnets now demand PoH, slashing sybil drains methodically.
Comparison of Leading PoH Protocols
| Protocol | Biometric Method | ZK Tech | Key Use Cases | Adoption |
|---|---|---|---|---|
| Humanity Protocol | Palm, Fingerprint, Facial | zk-SNARKs, zkProofers | Faucets, DAOs, Sybil Resistance | 120+ projects, 100+ dApps 🚀 |
| Rarimo | Multi-provider (e.g., Civic) | ZK Aggregator | dApp Plug-ins, Bot Prevention | Partnerships with Gitcoin Passport, Civic, Unstoppable Domains |
| zkTLS | Web Access Proof (non-biometric) | zkTLS | Privacy-Preserving Verification, Web3 Trust | No infra changes, Web2-Web3 Integration |
Rarimo’s aggregator shines in interoperability. By fusing Unstoppable Domains, Gitcoin Passport, and Civic, it crafts a unified proof of humanity zk layer. Users prove personhood once, reusing across ecosystems. This modular approach sidesteps silos, fostering a cohesive Web3 identity fabric.
Regulatory shadows loom, too. Centralized biometrics invite scrutiny, but decentralized ZK models diffuse liability. Verifiers earn H tokens for honest work, aligning incentives conservatively. Much like duration matching in bonds, these systems hedge against adversarial exploits, prioritizing resilience over speculative yields.
Real-World Applications: From Faucets to Governance
In practice, zero knowledge proof human verification transforms high-stakes entry points. Testnet faucets, once bot magnets, now gatekeep via Self Protocol’s PoH. Grants evade wallet farms through Human Passport’s detections. DAOs enforce one-person-one-vote with ZK uniqueness, restoring governance integrity.
DeFi platforms experiment boldly. Lenders verify borrower humanity sans credit histories, reducing default risks through sybil-proof collateral pools. Oracles like Chainlink integrate ZK identity, attesting data sources’ human origins. zkTLS bridges Web2-Web3, proving KYC or age without leaks, ideal for compliant NFTs or social dApps.
Proof of Personhood protocols proliferate. Identity Management Institute notes dApps flocking to zk-based PoP for authentic participation. Cube Exchange frames sybil resistance as Web3 security bedrock, limiting pseudonymous overreach. These tools do not just defend; they enable novel primitives, like human-curated signal markets or collaborative AI training sets.
Methodical evolution defines this space. Humanity Protocol’s palm biometrics, paired with ZKPs, generate tamper-evident uniqueness proofs on its verifier network. The H token not only fuels operations but empowers governance, letting stakeholders calibrate verifier incentives. zkProofers, as consensus linchpins, validate claims with cryptographic precision, purging botnets ecosystem-wide.
Web3 matures through such safeguards. Privacy proof of humanity web3 elevates interactions from anonymous chaos to verified equity. Projects like these recalibrate power dynamics, ensuring real humans, not algorithms, steer decentralized futures. Developers, armed with plug-ins and toolkits, embed these defenses natively, yielding resilient applications that withstand volatility. The prudent path forward lies in layered verification: biometrics for anchors, ZK for proofs, consensus for trust. Ecosystems thus fortified invite broader participation, preserving capital in the form of user confidence while unlocking sustainable growth.







