ZK Proofs for Proof-of-Humanity: Privacy-Preserving Identity Verification in Web3 2026

In the Web3 ecosystem of 2026, zero-knowledge proofs have become indispensable for tackling Sybil attacks and bot proliferation while upholding user privacy. These cryptographic tools allow individuals to demonstrate their humanity without exposing personal details, fostering trust in decentralized applications from DeFi to social platforms. Projects like Humanity Protocol’s zkProofers exemplify this shift, rewarding nodes for validating identities through zk proofs proof of humanity mechanisms.

Traditional identity systems often demand invasive data sharing, inviting risks of breaches and surveillance. Zero-knowledge proofs invert this paradigm. A user proves attributes, such as uniqueness or age, via mathematical commitments that reveal nothing beyond the claim’s validity. This zero knowledge identity verification underpins proof-of-humanity protocols, ensuring one person, one account, without centralized gatekeepers.
Humanity Protocol’s zkProofers Lead the Charge
Humanity Protocol has pioneered zkProofers, specialized nodes integral to its Proof of Humanity consensus. These nodes employ zero-knowledge proofs to confirm user genuineness via palm scans converted into non-revealing attestations. No biometric data persists onchain; instead, zk-proofs certify uniqueness. Participants earn $HP tokens, incentivizing network security and Sybil resistance.
This approach scales efficiently. As of March 2026, zkProofers enhance Web3 experiences by distinguishing humans from AI agents, a critical need amid rising bot activity. Their integration promises robust, privacy-first authentication across dApps.
Advantages of zkProofers
-

Sybil Resistance Without Data Leaks: zkProofers use ZKPs to verify genuine users in Humanity Protocol’s PoH without revealing identities or personal data.
-
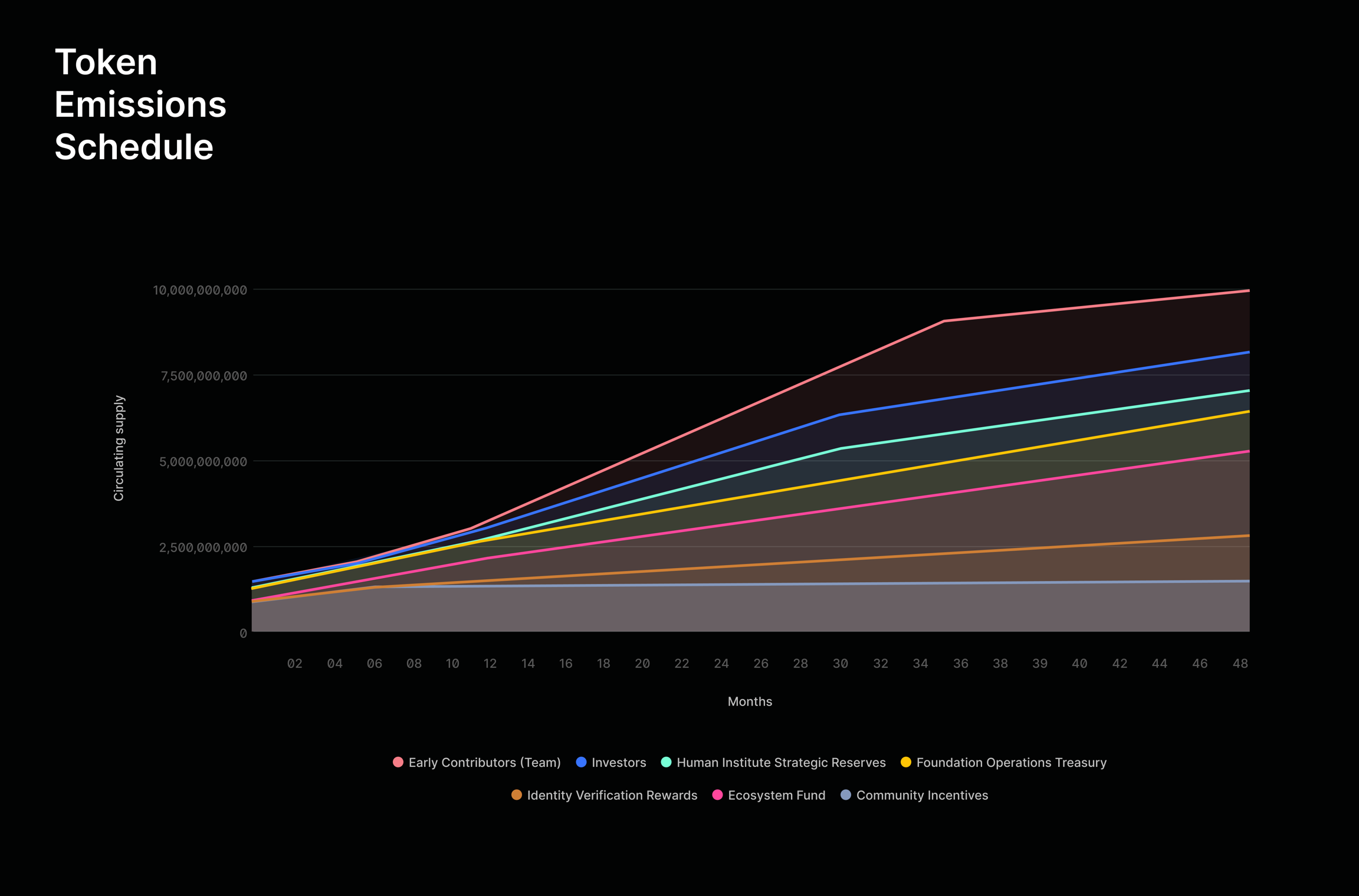
Token Rewards for Verifiers: zkProofers earn $HP tokens for validating identities and contributing to the network.
-
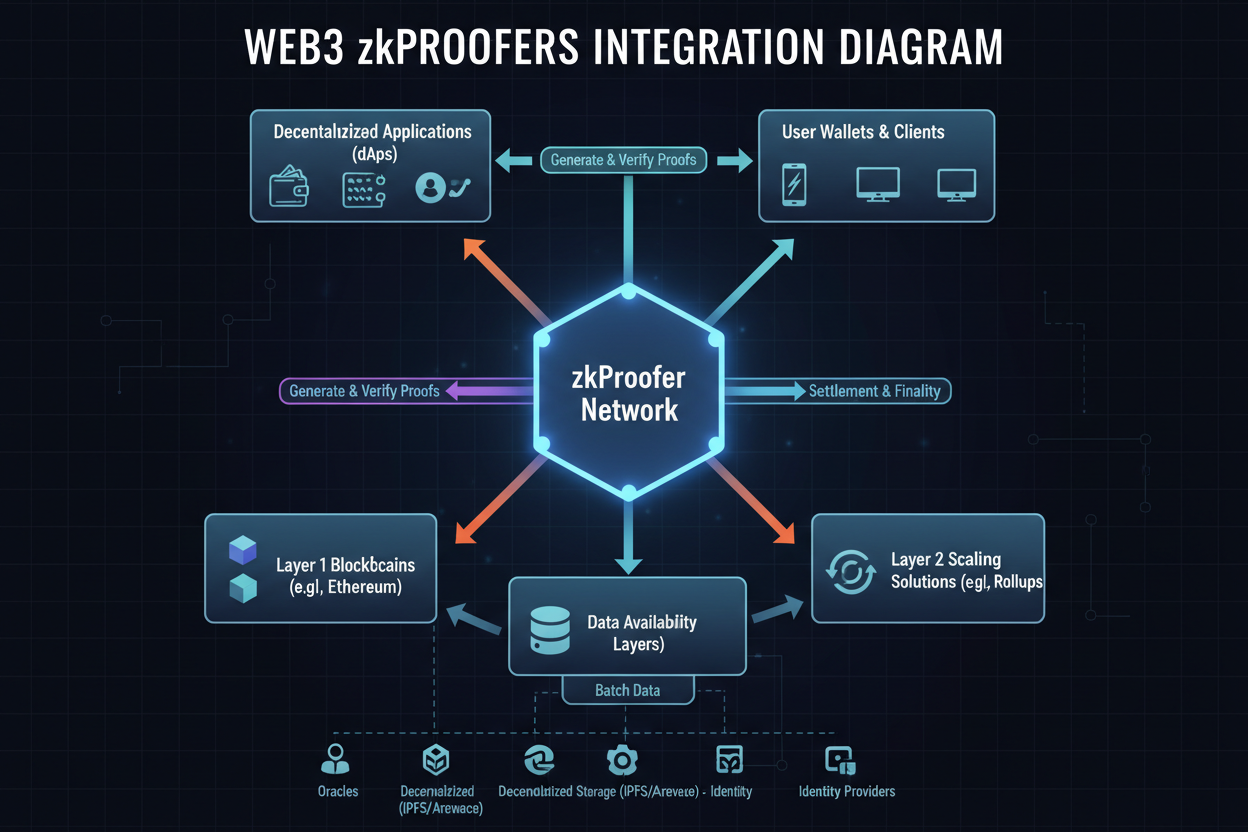
Seamless Web3 Integration: zkProofers fit into Humanity Protocol’s PoH consensus for easy Web3 dApp deployment.
-

Enhanced Security Against Bots: zkProofers distinguish humans from bots via privacy-preserving ZKPs.
Rarimo and Aggregated Proofs for Broader Adoption
Rarimo’s Proof of Humanity aggregator, partnering with Unstoppable Domains, Gitcoin Passport, and Civic, deploys zk-proofs to plug into Web3 dApps effortlessly. Developers embed this verification layer, allowing users to prove humanness sans repeated checks. It aggregates signals into a single zk-proof, streamlining trustless interactions.
Complementing this, ZK-ID tackles age verification. Users attest to being over 18 without disclosing names or birthdates, meeting regulatory demands in gaming and finance while preserving anonymity. Such targeted applications demonstrate privacy preserving proof of humanity in action.
Academic and Framework Innovations Bolster Scalability
Research advances like ZK-PoP analyze behavioral biometrics under zero-knowledge constraints, verifying human authorship without data exposure. Meanwhile, ZeroVision fuses steganography, neural networks, zk-SNARKs, and blockchain for iris authentication, prioritizing privacy in high-stakes scenarios.
The ZK-AMS framework addresses admission control, merging credential proofs with recursive aggregation for scalable Web3 services. Intract’s PoH, verifying over 100,000 users in minutes, slashes duplicate fingerprints by 400%, underscoring practical efficacy. These developments signal a maturing field where zk credentials web3 enable sybil resistant zk identity at scale.
DeFi platforms like Aave integrate similar Self zk proof-of-humanity solutions, prioritizing verified humans. This trend extends to confidential transactions, where proofs unlock access without identity compromise. As adoption grows, expect zk-proofs to redefine onchain governance and airdrops, curbing exploitation.
Yet despite these strides, deploying zk proofs proof of humanity involves trade-offs. Computational overhead from proof generation remains a hurdle, though recursive SNARKs and hardware optimizations are mitigating this. User friction in initial verification also persists, but protocols like Intract’s five-minute process show feasibility at scale.
Interoperability and Ecosystem Growth
Standardization efforts will dictate long-term success. Aggregators like Rarimo bridge disparate systems, fusing Gitcoin scores, Civic passes, and domain ownership into unified zero knowledge identity verification proofs. This modularity empowers developers to layer sybil resistant zk identity atop existing dApps without overhauls.
Consider governance applications. DAOs leverage these proofs for quadratic voting, ensuring one-human-one-vote integrity. Social platforms curb spam, while NFT drops reward genuine collectors. Each use case reinforces privacy preserving proof of humanity, aligning incentives with authenticity.
In my view, shaped by decades assessing risks in volatile markets, this technology mirrors prudent capital preservation: safeguard the principal, your identity, before chasing yields. ZK proofs minimize exposure while maximizing utility, a methodical hedge against digital threats.
Regulatory Alignment and Enterprise Potential
Regulators increasingly nod toward privacy tech. ZK-ID’s age gates comply with age-appropriate design codes sans data hoarding, paving enterprise adoption. Banks eye zk credentials web3 for KYC-lite, proving verification status without dossier dumps.
Challenges linger in proof universality. Behavioral ZK-PoP risks false positives from mimicry, while biometric hashes demand robust entropy. Yet frameworks like ZeroVision, blending AI with zk-SNARKs, fortify defenses. Methodical iteration, not hype, will refine these tools.
Aave’s pivot underscores momentum. By embedding Self’s zk layer, it gates high-value features to humans, slashing bot exploits. Parallel integrations in lending pools and yield farms signal DeFi’s maturation, where privacy isn’t optional but foundational.
Zero-knowledge proofs transform identity from liability to asset, verifiable yet veiled.
Looking ahead, 2026 marks inflection. With zkProofers scaling rewards and aggregators plugging gaps, Web3 edges toward humane decentralization. Projects converge on palm, iris, behavior signals, all funneled through ZK circuits for seamless proofs.
Stakeholders must prioritize audited circuits and oracle decentralization to avert centralization creep. As adoption swells, so does the imperative for rigorous verification. In this arena, conservative deployment trumps reckless scaling; verify first, expand second.
Ultimately, these innovations equip Web3 with defenses akin to fortified vaults: impenetrable to intruders, transparent in function. Users reclaim sovereignty, proving humanity on their terms. The era of anonymous bots fades, yielding to a trusted, private digital commons.







