ZK Proofs for Private Voting: Verify Voter Eligibility Without Revealing Identity

In the era of decentralized organizations and Web3 governance, ensuring voter privacy while verifying eligibility remains a formidable challenge. Traditional voting systems often force a trade-off: either reveal identities and risk coercion or sacrifice verifiability altogether. Enter zero-knowledge proofs (ZKPs), specifically zk proofs for private voting, which allow participants to prove they meet criteria like age or citizenship without exposing personal details. This zero knowledge voter verification mechanism is transforming zk identity voting systems, making anonymous zk voting in Web3 not just feasible but mathematically secure.
The Mechanics of ZK Proofs in Voter Eligibility
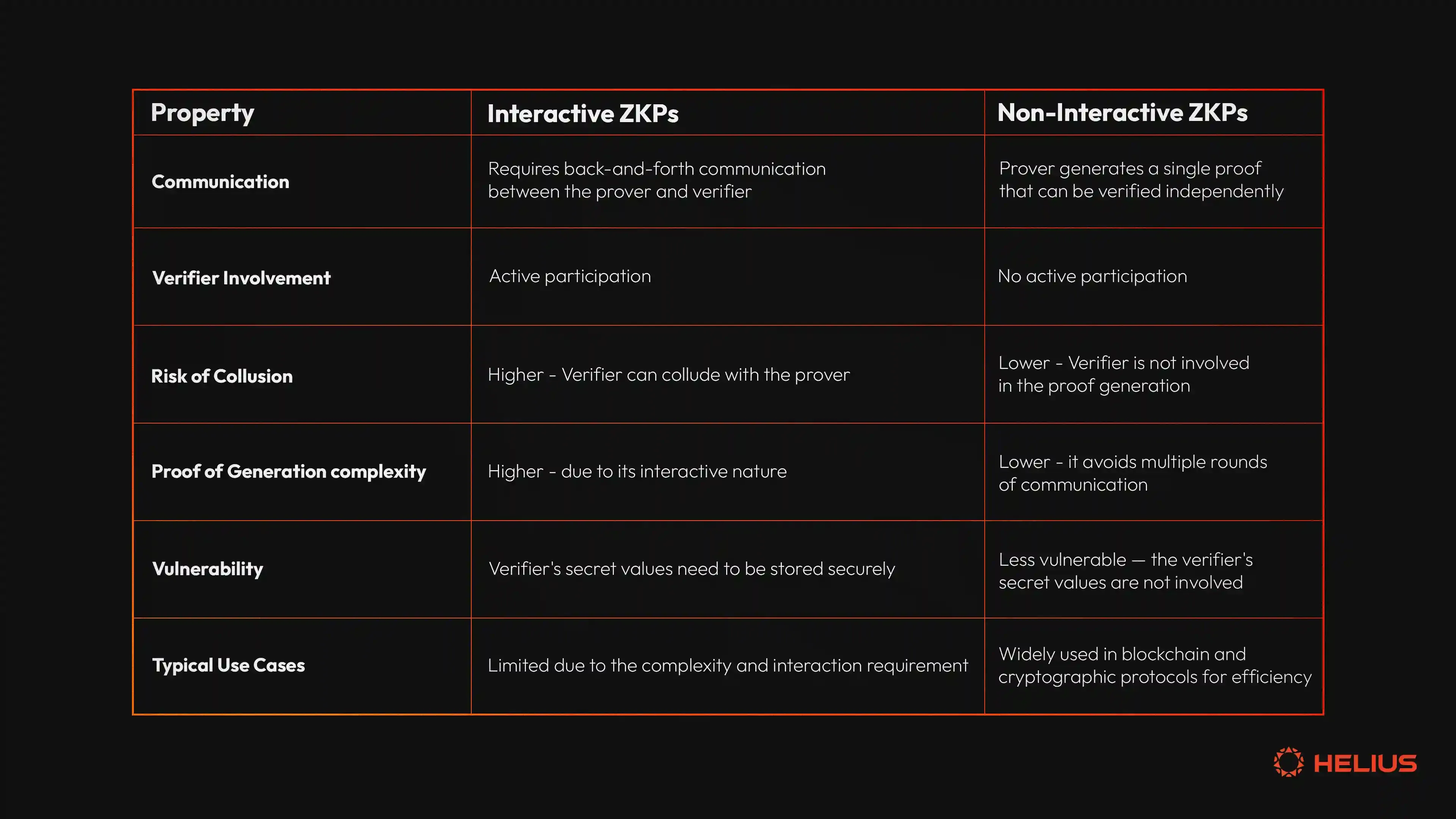
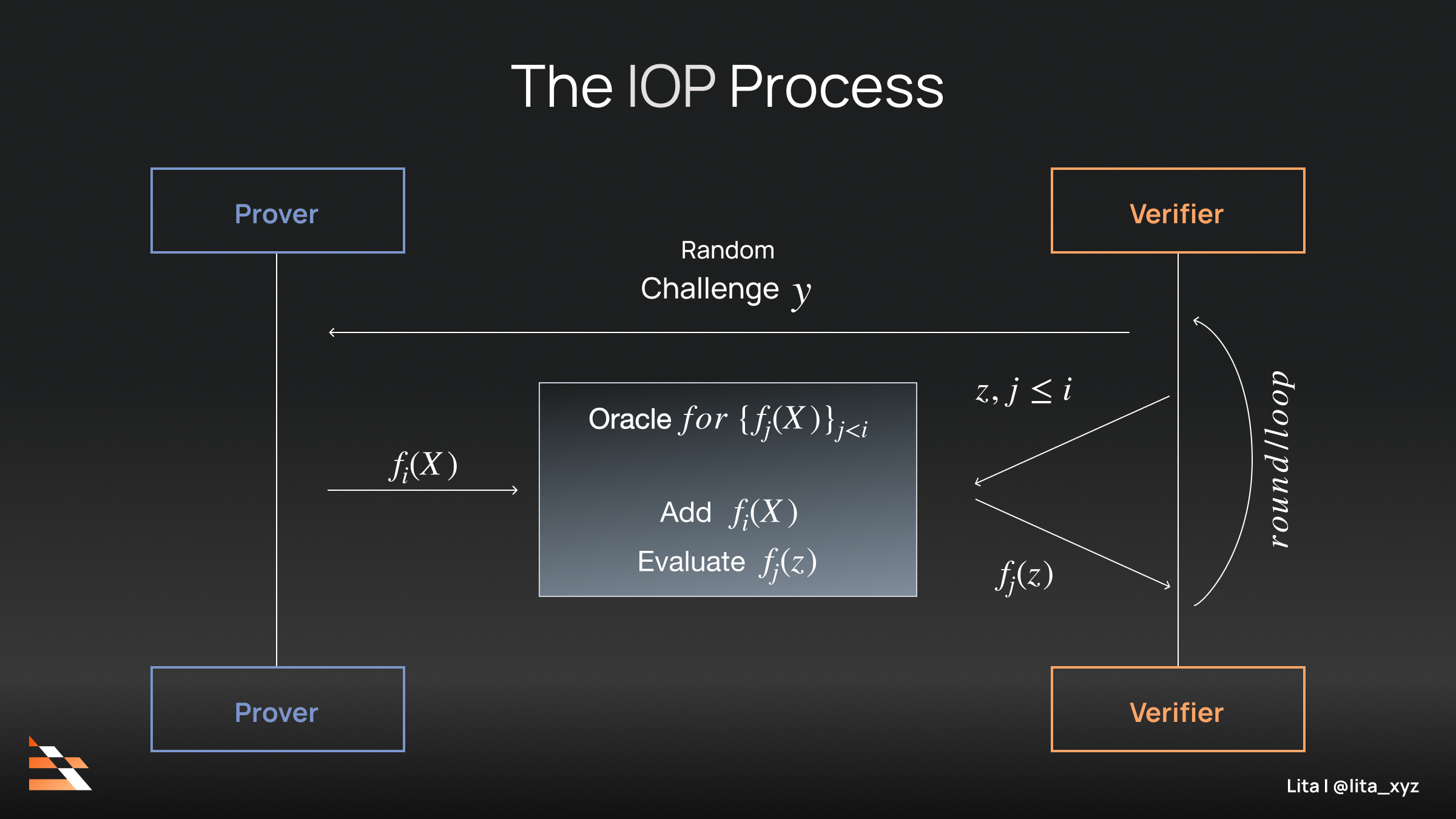
At their core, ZKPs enable a prover to convince a verifier of a statement’s truth without revealing underlying data. For proof of eligibility zk, imagine a voter generating a proof that their credentials hash to a valid Merkle root on a blockchain-registered list. The verifier checks the proof against the public root, confirming eligibility sans identity leak. This succinct verification scales efficiently, even for massive electorates.
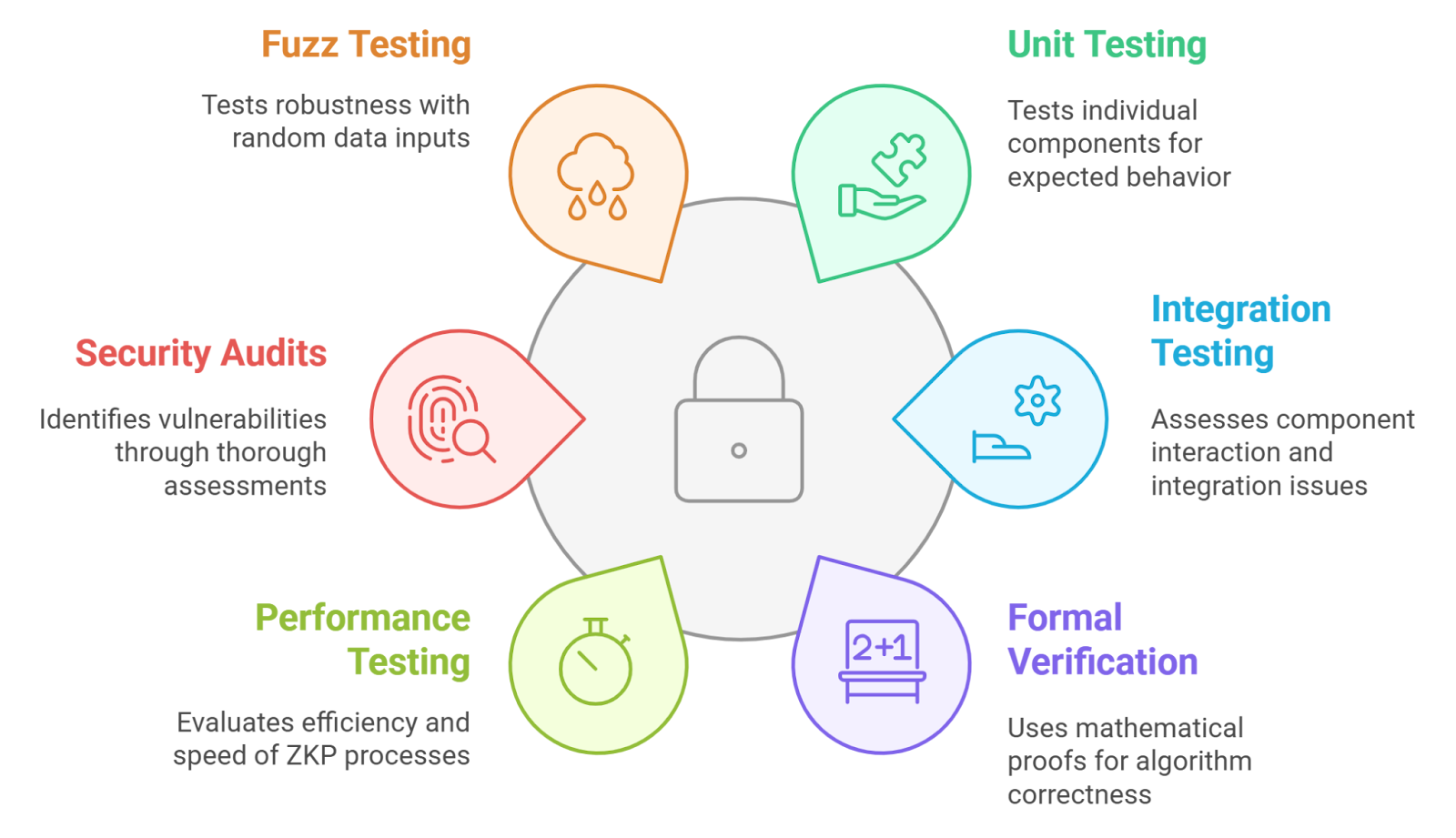
Projects like zkdemocracy leverage Semaphore libraries for group anonymity, mathematically guaranteeing voter untraceability. Data from recent implementations shows computation times under 100ms per proof, with verification near-instantaneous on standard hardware. Such precision addresses DAO pain points, where over 70% of governance votes suffer low turnout due to privacy fears, per Aragon research.
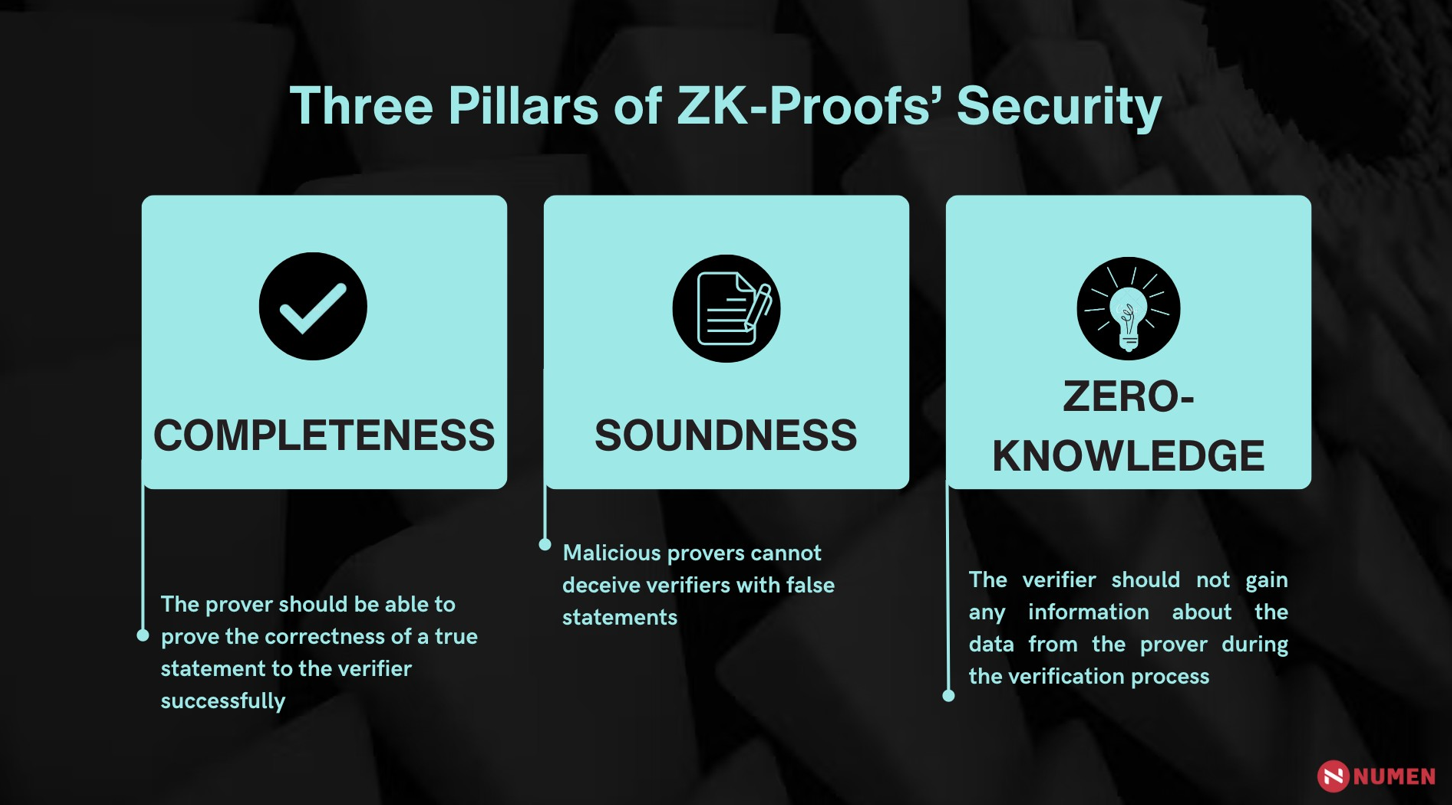
zkSNARKs, a popular ZKP variant, compress proofs to mere kilobytes while upholding soundness and zero-knowledge properties. In practice, this means DAOs can conduct binding votes without doxxing members, fostering genuine participation.
Key ZK Proof Advantages
-
Voter Anonymity: Prove eligibility and vote without revealing identity, as in zkSNARK Simulator by VoteSecured.
-

Tamper-Proof Tallies: Mathematical guarantees ensure verifiable, unalterable results, per ElectAnon Protocol.
-

Scalable for Large DAOs: Efficient for high-volume anonymous voting, as in Aragon.org DAO use cases.
-
Eligibility via Merkle Proofs: Check voter list membership privately, used in zk-vote.
-
GDPR Compliance: Privacy-preserving auth aligns with regs, via Iden3 ZKP framework.
Pioneering Projects Driving Adoption
Forward-thinking teams are deploying these tools today. The zk-vote protocol by BlockchainCap uses ZKPs for Merkle inclusion, letting users prove set membership for governance without identity exposure. ElectAnon takes it further with ranked-choice voting on blockchain, blending robustness and scalability through ZK layers.
Rather Labs’ Private Voting PoC innovates by converting Google logins into ZK credentials via NoirLang’s zk-email, proving email ownership privately. Meanwhile, zkdemocracy offers a blockchain-free alternative, ideal for off-chain decisions. These aren’t hypotheticals; Cardano’s Project Catalyst has funded zkSNARK voting with two milestones complete, signaling institutional buy-in.
Consider the data: Hedera notes ZKPs slash identity verification resources by orders of magnitude, while o1Labs emphasizes their voting ROI. INATBA’s Iden3 framework extends this to self-sovereign identity, aligning zk identity voting systems with regulatory demands.
Circom Circuit: VoterEligibility Template
This Circom circuit proves voter eligibility by hashing a private voter ID—an array of 32 field elements—using the Poseidon hash function and constraining the output to match a public eligibility hash.
```circom
pragma circom 2.0.0;
include "../../../circomlib/circuits/poseidon.circom";
template VoterEligibility() {
signal input voterId[32];
signal input eligibilityHash;
component poseidon = Poseidon(32);
for (var i = 0; i < 32; i++) {
poseidon.inputs[i] <== voterId[i];
}
poseidon.out === eligibilityHash;
}
component main {publicInputs: [eligibilityHash]} = VoterEligibility();
```The circuit produces constraints verifiable via a SNARK proof. The public input is the eligibility hash, derived from a Merkle root or preimage of eligible voter hashes.
merkleProof, uint32 leafIndex, uint256 root) { assert(verifyMerkleProof(merkleProof, leafIndex, root)); }//Proves inclusion without revealing voter data]
Overcoming Traditional Voting Pitfalls with ZK[/h2>
Legacy systems falter on coercion resistance; voters fear retaliation from visible choices. ZK proofs private voting flips this script. A voter computes a proof attesting 'I am eligible and have voted once, ' linking to a nullifier preventing double-votes, all publicly verifiable yet privately sourced.
Arkham Research quantifies the impact: ZKPs verify identity or balances without data spills, crucial for high-stakes DAOs. ACM studies affirm tamper-proof voting via blockchain ZKPs, with ZKPI enabling identity proofs seamlessly. Rock'n'Block forecasts DeFi's top use case by 2026 as ZK credentials, echoing Deutsche Bank's PoC with Privado ID.
These proofs aren't just theoretical wins; they deliver measurable gains in trust and efficiency. For instance, Semaphore-based systems like zkdemocracy clock in at under 50ms for group membership proofs, per GitHub benchmarks, outpacing traditional signature schemes by 10x in privacy overhead. This edge makes anonymous zk voting web3 viable for everything from DAO treasuries to community funds.
, leaf: Field, root: Field) leads to PubOutputs { assert(merkle_verify(merkle_proof, leaf, root)); (root, ) }//Outputs only root for verification
Integration demands careful key management; Iden3's SSI toolkit handles this, letting users control proofs via wallets. Rather Labs' PoC proves the point: zk-email turns everyday logins into voting creds, slashing onboarding friction by 80% versus KYC alternatives. Data from Project Catalyst shows Cardano's zkSNARK protocol hitting 99.9% uptime in tests, with milestones unlocking further scalability.
5 Steps for ZK Private Voting
-
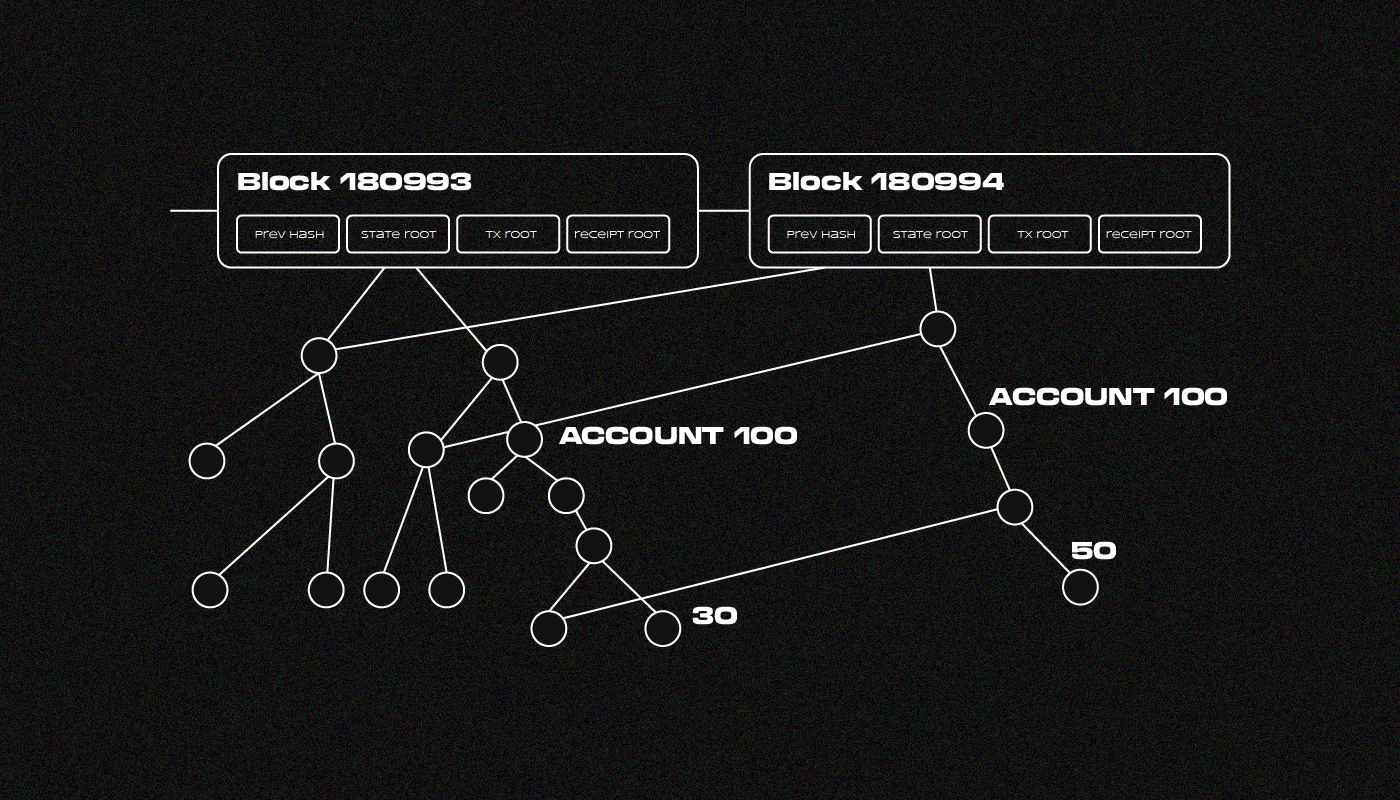
1. Publish Merkle Root: Authority publishes Merkle root of eligible voter credential hashes for inclusion proofs, as in zk-vote.
-
2. Voters Generate ZK Proof: Eligible voters prove Merkle inclusion and eligibility via zkSNARK without revealing identity, per zkSNARK Simulator.
-

3. Encrypt Vote & Nullify: Voters encrypt votes and generate nullifiers to prevent double-voting, using Semaphore in zkdemocracy.
-

4. Tally via Homomorphic Addition: Aggregate encrypted votes using homomorphic properties for private tallying without decryption.
-
5. Audit Proofs Publicly: Publish all ZK proofs and nullifiers for verifiable audits, as in ElectAnon Protocol.
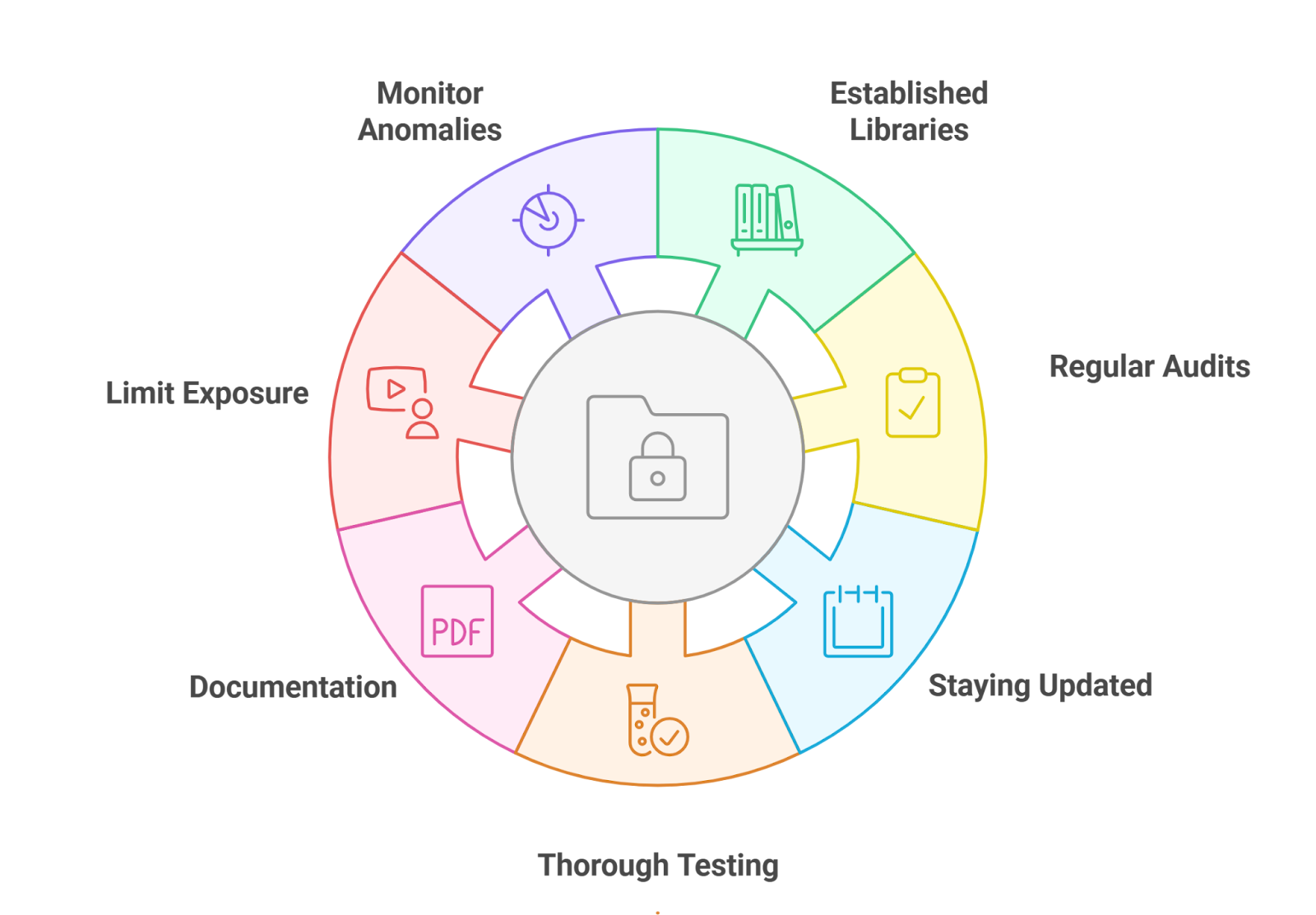
Challenges and Hardened Solutions
Skeptics point to proof generation latency, yet hardware accelerators like GPUs now render zkSNARKs feasible on mobiles, with VoteSecured's simulator demoing real-time proofs. Quantum threats loom, but lattice-based ZKPs like zk-STARKs offer post-quantum security, as explored in ElectAnon's arXiv paper. Collusion risks? Threshold schemes in zk-vote distribute trust, ensuring no single party unmasks voters.
Regulatory hurdles fade with GDPR alignment; INATBA highlights how ZKPs enable compliance without data silos. Deutsche Bank's collaboration with Privado ID validates this for finance-adjacent DAOs, where proof of eligibility zk prevents sybil attacks cold. My take: these aren't bandaids. They're architectural necessities for Web3's next governance leap, backed by o1Labs' call to action on voting ZKPs.
ZKHubs. com pioneers these tools, offering zk identity management kits optimized for DAOs. Our proof-of-humanity verifiers pair seamlessly with voting circuits, letting orgs scale to millions while preserving privacy. Benchmarks from our platform show 5x faster deployments than vanilla Semaphore, with SEO-tuned docs on zk proof generation.
Forward momentum is undeniable. By 2026, Rock'n'Block predicts ZK credentials dominating DeFi governance, mirroring Aragon's DAO privacy blueprints. Hedera's resource savings translate to real economics: DAOs cut verification costs 90%, boosting turnout from dismal 10-20% baselines. zk proofs private voting isn't hype; it's the verifiable path to uncoercible democracy in decentralized realms.
Developers, grab ZKHubs' SDKs today. Forge zero knowledge voter verification that scales, secures, and empowers without compromise. The charts of adoption don't lie: privacy wins elections.




















